Sybil Attack Examples in Cryptocurrency: How Fake Identities Break Blockchains

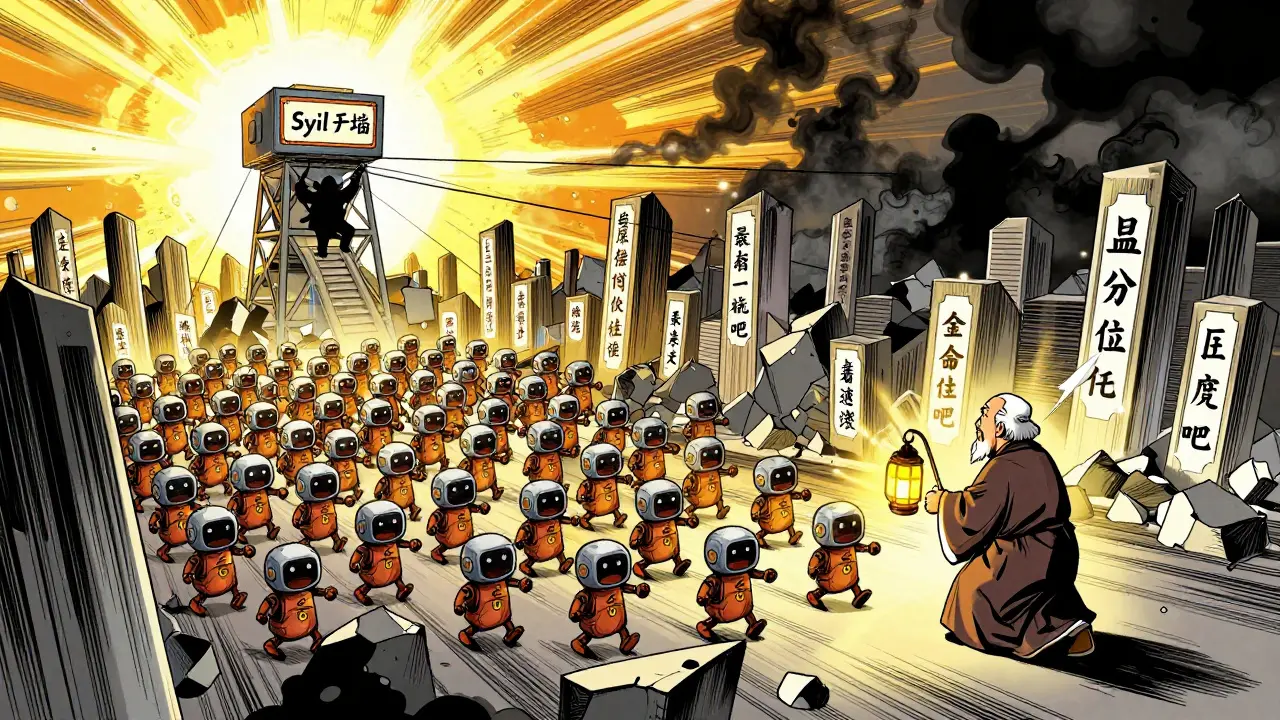
Imagine a voting system where one person can cast 10,000 votes. That’s what a Sybil attack does to a cryptocurrency network. Instead of real users, attackers flood the system with fake identities-thousands of fake wallets, each pretending to be a separate person. They don’t need to steal your private key. They just need to look like enough legitimate users to take control. And it’s happened. More than once.
What Exactly Is a Sybil Attack?
The term comes from the 1973 book Sybil, about a woman with 16 personalities. In crypto, it means one attacker pretending to be dozens, hundreds, or even thousands of people. Blockchain networks rely on decentralization: no single entity should control the system. But if you can create a ton of fake nodes or wallets, you start to look like the majority. And when you look like the majority, you start to control it.
Cryptocurrencies are built on pseudonymity, not anonymity. That means you don’t need to give your real name to join. You just need a wallet. That’s great for privacy-but it’s a gift to attackers. A bot can generate 50,000 wallets in under an hour. Fund them with a few dollars in ETH or BTC. Then use them to interact with DeFi apps, claim airdrops, or vote in DAOs. Suddenly, you’re not one bad actor. You’re 50,000 "users."
How Sybil Attacks Actually Work
It’s not magic. It’s automation.
- **Wallet farming**: Attackers use scripts to create thousands of wallets. Each one gets a tiny amount of crypto to pay for transaction fees-enough to look real.
- **Liquidity farming**: They deposit small amounts into DeFi pools to qualify for token rewards. The more wallets, the more rewards.
- **Governance manipulation**: In DAOs, voting power often depends on token holdings. Fake wallets with low-value tokens can still vote. Combine thousands of them, and you can pass proposals that steal treasury funds or change protocol rules.
- **Node isolation**: On peer-to-peer networks, attackers connect directly to honest nodes and flood them with fake peers. This cuts off the real network, making it easier to feed false data.
- **Whitewashing**: When one batch of wallets gets flagged and banned, attackers just create a new batch. Rinse and repeat.
It’s cheap. It’s scalable. And until recently, most networks had no way to tell the difference between a real user and a bot.
Real-World Sybil Attack Examples
Ethereum Classic (ETC) - August 2020
This was the most damaging Sybil attack in crypto history. Attackers didn’t just create fake wallets-they took over mining. By controlling over 51% of the network’s hash power (a form of Sybil attack on mining nodes), they reversed transactions, double-spent coins, and stole over $5 million. The attack happened multiple times over weeks. Ethereum Classic had to hard-fork to fix it. The damage? Lost trust. Lost users. And a permanent scar on the network’s reputation.
Verge (XVG) - 2018-2020
Verge promised privacy. But its Proof-of-Work algorithm was weak. Attackers used botnets to control mining nodes and created fake identities across the network. They manipulated transaction confirmations, stole coins, and disrupted the entire blockchain. The project never fully recovered. Today, Verge trades at less than 1% of its all-time high.
DeFi Airdrop Exploits - 2021-2024
Dozens of DeFi protocols launched token airdrops to reward early users. But bots got there first. One project, $UNI, saw 40% of its initial airdrop claims come from wallets that had never interacted with the protocol before. Attackers used IP rotation, device spoofing, and wallet clustering to fake engagement. The result? Real users got smaller shares. The project’s token price dropped 18% in 48 hours after the exploit went public.
DAO Voting Manipulation - 2023
A decentralized autonomous organization (DAO) managing a $200 million treasury held a vote on whether to fund a new development team. The proposal passed 67% to 33%. But audit logs later showed that 89% of the "yes" votes came from wallets created in the last 72 hours. None had any history of participation. The DAO had to reverse the vote, but the damage was done-community trust was broken.
Why Some Blockchains Are More Vulnerable
Not all blockchains are equal when it comes to Sybil resistance.
Bitcoin is hard to attack because of Proof-of-Work. To create a fake mining node, you need real hardware, electricity, and time. The cost to control 1% of Bitcoin’s network is over $10 billion in equipment and energy. It’s cheaper to mine honestly.
Ethereum switched to Proof-of-Stake. That changed everything. Now, instead of buying GPUs, attackers just need to stake ETH. But staking requires 32 ETH-about $100,000. That’s expensive, but not impossible. So Ethereum uses slashing: if you act maliciously, you lose your stake. It’s economic deterrence, not computational.
Smaller chains like Polygon PoS, Solana, or BNB Chain are more vulnerable. Their staking requirements are low. Their validator sets are small. And their security budgets? Nonexistent. Attackers can rent cheap cloud servers, create hundreds of validator nodes, and take over consensus. That’s why you see more reorgs and double-spends on these networks.
How Networks Are Fighting Back
Defense isn’t about stopping every fake wallet. It’s about making it too expensive to matter.
- Quadratic voting: Instead of one token = one vote, your voting power is the square root of your holdings. So if you hold 100 tokens, you get 10 votes. If you hold 10,000, you get 100. This stops whales and Sybil farms from dominating.
- Reputation-based systems: Projects like Gitcoin and Ethereum Name Service give more weight to users who’ve been active for years. A wallet that’s been around since 2019 counts more than one created yesterday.
- Token-gated access: Some DAOs require you to hold a specific NFT or complete a KYC check to vote. It’s not perfect, but it raises the barrier.
- On-chain behavior analysis: New tools track wallet behavior. Does a wallet only swap tokens? Does it never send to other addresses? Does it create 50 wallets in 10 minutes? Those are red flags.
Chainlink’s oracle network doesn’t just rely on price feeds-it uses a reputation layer. Nodes with a history of accurate data get more weight. Nodes that lie get penalized. That’s Sybil resistance built into the protocol.

Why This Matters Beyond Theft
Sybil attacks aren’t just about stolen coins. They break trust.
- Broken finality: If attackers can reverse transactions, no one can trust that their money is safe.
- Corrupted governance: When bots control DAO votes, the community loses its voice.
- Privacy leaks: Fake wallets can be used to map real users’ IP addresses and transaction patterns.
- Network fragmentation: When nodes are isolated, the blockchain becomes unreliable.
These aren’t theoretical risks. They’re happening now. And every time a network gets hacked through Sybil, more users leave. More investors panic. More regulators step in.
What You Can Do
If you’re a user:
- Avoid projects that hand out free tokens with zero requirements. They’re bait for Sybil farms.
- Check if a DAO has reputation or quadratic voting. If not, its governance is likely compromised.
- Use wallets with history. A wallet that’s been used for 2 years is safer than a new one.
If you’re a developer:
- Don’t rely on simple token balances for voting.
- Implement on-chain behavior checks.
- Use decentralized identity solutions like ENS or Soulbound Tokens.
Sybil attacks will keep evolving. But so will the defenses. The difference between a secure blockchain and a broken one? It’s not code. It’s incentives. If it’s cheaper to attack than to participate, the system fails. If participation is more rewarding than cheating, it survives.
Can a Sybil attack steal my crypto directly?
Not directly. A Sybil attack doesn’t hack your wallet or guess your private key. Instead, it manipulates the network to reverse transactions, double-spend coins, or steal from protocols like DeFi pools. Your funds are safe as long as the network stays honest. But if attackers control consensus, they can make it look like your transaction never happened.
Is Bitcoin immune to Sybil attacks?
Bitcoin is highly resistant, but not immune. Because of Proof-of-Work, creating a fake mining node requires massive computational power. The cost to control even 1% of Bitcoin’s network is billions of dollars. It’s far cheaper to mine legitimately. So while technically possible, a Sybil attack on Bitcoin is economically irrational.
Why do DeFi projects get targeted by Sybil attacks?
Because they hand out free money. Airdrops, liquidity mining rewards, and governance tokens are valuable. Attackers create thousands of fake wallets to claim them. The more wallets they control, the more tokens they steal. This isn’t just about stealing-it’s about distorting the entire incentive structure of the protocol.
Can a Sybil attack affect my NFT collection?
Yes. If your NFT project has a DAO or voting system for future drops, roadmap changes, or treasury spending, attackers can create fake wallets to vote. They might push through a proposal that gives them control of future NFT mints or drains the project’s funds. Projects using simple token-weighted voting are most at risk.
Are there any blockchains that are completely Sybil-proof?
No. There’s no such thing as a completely Sybil-proof system. But some are far more resistant. Networks that combine economic costs (like staking), reputation (like long-term activity), and social verification (like KYC or community approval) are the hardest to attack. Bitcoin and Ethereum are the most secure today-not because they’re perfect, but because the cost to attack them is too high to be worth it.
Heather James
March 14, 2026 AT 12:03Sarah Hammon
March 14, 2026 AT 19:49iam jacob
March 16, 2026 AT 01:55Ann Liu
March 16, 2026 AT 15:12Dionne van Diepenbeek
March 18, 2026 AT 13:22Graham Smith
March 19, 2026 AT 06:08Jerry Panson
March 20, 2026 AT 14:57Katrina Smith
March 21, 2026 AT 02:21Anastasia Danavath
March 21, 2026 AT 03:49Angelica Stovall
March 22, 2026 AT 10:51